Azure PostgreSQL (Managed Identity)
Last modified on April 2, 2025
Overview
This guide describes how to set up managed identities in the Microsoft Azure portal and set up StrongDM to use them to connect to Azure Database for PostgreSQL. The Azure PostgreSQL (Managed Identity) datasource type supports both user-assigned and system-assigned managed identities to authenticate to Azure Database for PostgreSQL.
Prerequisites
- Ensure that you have access to an Azure subscription with appropriate permissions to create user-assigned managed identities.
- Have an Azure Virtual Machine (VM) with a StrongDM gateway or relay installed on it.
- Have an Azure account with the Virtual Machine Contributor and Managed Identity Operator role assignments in order to assign managed identities to your VM. Note that no other Microsoft Entra (formerly Azure AD) directory role assignments are required.
- Have at least one user-assigned managed identity already created, so you can assign it to the VM.
- Meet the following requirements for adding a datasource in the StrongDM Admin UI:
- Properly configure an account for your database resource. If you choose to store credentials for the resource with StrongDM, have those credentials ready. When not using StrongDM, set up a Secret Store integration and be able to enter the location of the secrets required to access the resource.
- The hostname or endpoint you enter for your resource must be accessible by at least one gateway or relay.
Azure Setup
The following steps provide general instructions on what to do within Azure. For more detailed information, please consult Microsoft Azure documentation:
- Managed Identity Setup for Azure Database for PostgreSQL Single Server
- Managed Identity Setup for Azure Database for PostgreSQL Flexible Server
User-assigned managed identity
If using a user-assigned managed identity, follow these steps.
- Sign in to the Azure portal. You must use an account associated with the Azure subscription that contains the Azure VM that hosts your gateway or relay.
- Assign a user-assigned managed identity to your VM.
- Copy the client ID of that user-assigned managed identity for use in later steps.
- Create a PostgreSQL user for the user-assigned managed identity. This can be done for Azure Database for PostgreSQL Single Server or Flexible Server.
- Set up roles and permissions (for example, read or readwrite) on your database for the managed identity. This must be done so that the StrongDM gateway or relay can connect to it using the managed identity assigned to the gateway or relay’s VM.
System-assigned managed identity
If using a system-assigned managed identity, follow these steps.
- Sign in to the Azure portal using an account associated with the Azure subscription that contains the Azure VM that hosts your gateway or relay.
- If the VM was provisioned without a system-assigned managed identity, enable the system-assigned managed identity by changing its status to On.
- Find the client ID of the system-assigned managed identity and copy it for use in later steps. The client ID may be obtained by using the Azure CLI, not the Azure portal, with
az ad sp list --display-name <VM_NAME> --query [*].appId --out tsv. - Create a PostgreSQL user for the managed identity. This can be done for Azure Database for PostgreSQL Single Server or Azure Database for PostgreSQL Flexible Server. Note that the “managed identity name” for the system-assigned identity is the name of the VM.
- Set up roles and permissions (for example, read or readwrite) on your database for the managed identity. This must be done so that the StrongDM gateway or relay can connect to it using the managed identity assigned to the gateway or relay’s VM.
StrongDM Admin UI Setup
To add Azure PostgreSQL (Managed Identity) as a StrongDM datasource in the Admin UI, use the following steps.
Log in to the Admin UI.
Go to Resources > Datasources.
Click Add datasource.
Select Azure PostgreSQL (Managed Identity) as the Datasource Type and set other configuration properties for your new database resource.
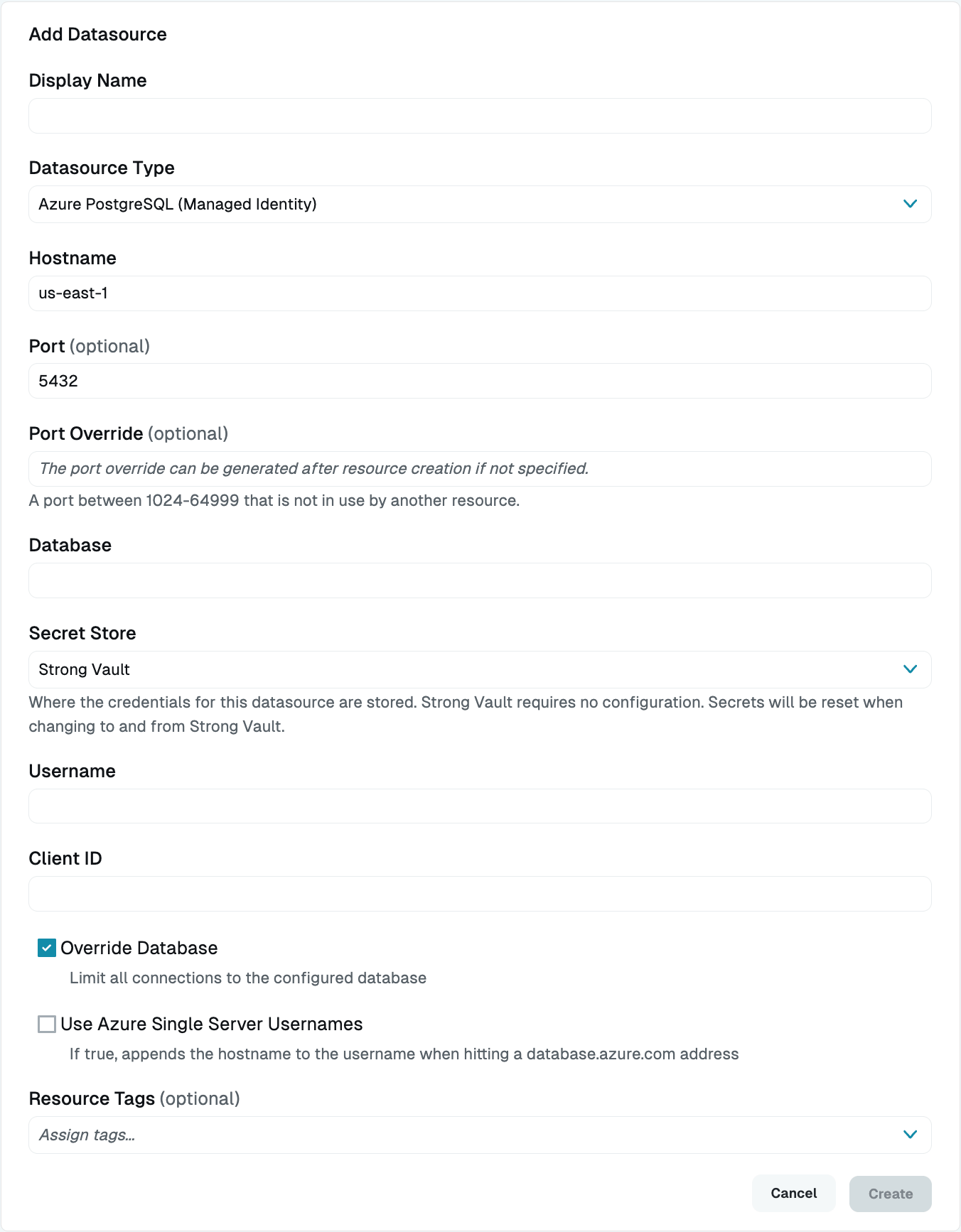
Add Azure PostgreSQL Datasource (Managed Identity) Complete all required fields.
Click Create to save the resource.
Click the resource name to view status, diagnostic information, and setting details.
Resource properties
Configuration properties are visible when you add a datasource or when you click to view its settings. The following table describes the settings available for your Azure PostgreSQL (Managed Identity) resource.
| Property | Requirement | Description |
|---|---|---|
| Display Name | Required | Meaningful name to display the resource throughout StrongDM; exclude special characters like quotes (") or angle brackets (< or >) |
| Datasource Type | Required | Select Azure PostgreSQL (Managed Identity) |
| Proxy Cluster | Required | Defaults to “None (use gateways)”; if using proxy clusters, select the appropriate cluster to proxy traffic to this resource |
| Hostname | Required | Hostname for your Azure PostgreSQL database resource; must be accessible to a gateway or relay |
| Port | Required | Port to use when connecting to your Azure PostgreSQL database; default port value is 5432 |
| Port Override | Read only | Automatically generated with a value between 1024-59999 as long as that port is not used by another resource; preferred port can be modified later under Settings > Port Overrides |
| Database | Required | Database name you would like to connect to using this datasource |
| Secret Store | Optional | Credential store location; defaults to Strong Vault; learn more about Secret Store options |
| Username | Required | Username of the PostgreSQL user for your managed identity, which you created during Azure setup |
| Client ID | Required | Client ID of your managed identity in the Azure portal |
| Username (path) | Required | Path to the secret in your Secret Store location (for example, path/to/credential?key=optionalKeyName where key argument is optional); required when using a non-StrongDM Secret Store type |
| Client ID (path) | Required | Path to the secret in your Secret Store location (for example, path/to/credential?key=optionalKeyName where key argument is optional); required when using a non-StrongDM Secret Store type |
| Override Database | Optional | By default, StrongDM limits all connections to the configured database. Uncheck the box to disable this option. If this option is deselected, the value entered in the Database field is only used for healthchecks, not for user connections. When accessing the database via StrongDM, users need to explicitly pass the database name they wish to connect to in the connection string. If they do not, the value of the Username field is passed in as the database name. This is the default behavior of the database type. |
| Use Azure Single Server Usernames | Optional | If selected, the hostname is appended to the username when interacting with a database.azure.com address |
| Resource Tags | Optional | Resource tags consisting of key-value pairs <KEY>=<VALUE> (for example, env=dev) |
Secret Store options
By default, datasource credentials are stored in StrongDM. However, these credentials can also be saved in a secrets management tool.
Non-StrongDM options appear in the Secret Store dropdown if they are created under Settings > Secrets Management. When you select another Secret Store type, its unique properties display. For more details, see Configure Secret Store Integrations.
Resource status
After a resource is created, the Admin UI displays that resource as unhealthy until the health checks run successfully. When the resource is ready, the Health icon indicates a positive, green status.
When the resource does not display a positive status, click the resource name to go to the Diagnostics tab and check for errors.