Microsoft SQL Server (Azure AD)
Last modified on April 2, 2025
Overview
A datasource consists of a database resource and the credentials used to access it. This guide describes how to add a Microsoft SQL Server (Azure AD) database as a datasource in the StrongDM Admin UI. This resource type only supports Azure Active Directory (AD) authentication. For other options, see the Microsoft SQL Server and Microsoft SQL Server (Kerberos) resource types.
Prerequisites
To add a datasource, make sure you have met the following prerequisites:
- Properly configure an account for your database resource. If you choose to store credentials for the resource with StrongDM, have those credentials ready. When not using Strong Vault, set up a Secret Store integration and be able to enter the location of the secrets required to access the resource.
- The hostname or endpoint you enter for your resource must be accessible by at least one gateway or relay. To verify this, log in to the gateway or relay and use the
nc -zv <YOUR_HOSTNAME> <YOUR_PORT>Netcat command. For example, usenc -zv testdb-01.fancy.org 5432. If your gateway server can connect to this hostname, you can proceed. - You need your Azure DB set up, app registration complete, and the intended user added to your Azure VM. If these steps are already done, the Azure Setup section can provide guidance.
-z flag to check for listeners without sending data and the -v flag to show verbose output. If you do not have Netcat, you can use a package manager such as APT (Advanced Package Tool) to install it. On Linux-based distributions, run apt-get install netcat.Add a Datasource
To add your new Microsoft SQL Server database as a StrongDM datasource, use the following steps.
Log in to the Admin UI.
Go to Resources > Datasources.
Click Add datasource.
Select Microsoft SQL Server (Azure AD) as the Datasource Type and set other configuration properties for your new database resource.
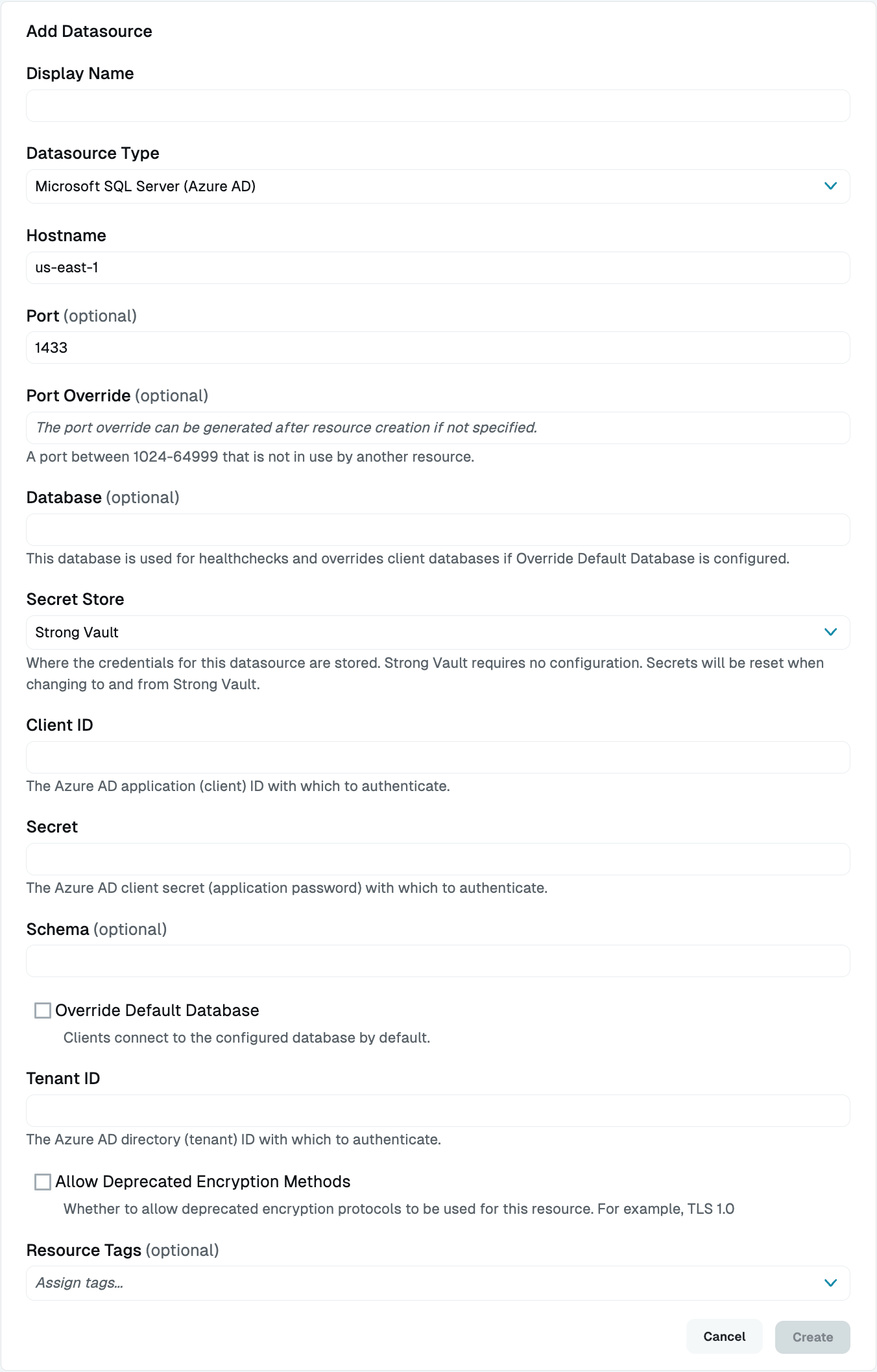
Add Microsoft SQL Server (Azure AD) Datasource Complete all required fields.
Click Create to save the resource.
Click the resource name to view status, diagnostic information, and setting details.
Resource properties
Configuration properties are visible when you add a datasource or when you click to view its settings. The following table describes the settings available for your Microsoft SQL Server database.
| Property | Requirement | Description |
|---|---|---|
| Display Name | Required | Meaningful name to display the resource throughout StrongDM; exclude special characters like quotes (") or angle brackets (< or >) |
| Datasource Type | Required | Select Microsoft SQL Server (Azure AD) |
| Proxy Cluster | Required | Defaults to “None (use gateways)”; if using proxy clusters, select the appropriate cluster to proxy traffic to this resource |
| Hostname | Required | Hostname for your Microsoft SQL Server database resource; must be accessible to a gateway or relay |
| Port | Required | Port to use when connecting to your Microsoft SQL Server database; default port value is 1433 |
| Port Override | Read only | Automatically generated with a value between 1024-59999 as long as that port is not used by another resource; preferred port can be modified later under Settings > Port Overrides |
| Database | Required | Database name you would like to connect to using this datasource |
| Secret Store | Optional | Credential store location with the default set to Strong Vault; learn more about Secret Store options |
| Client ID | Required | Application (Client) ID value from app registration |
| Secret | Required | Microsoft Entra (formerly Azure AD) client secret (application password) with which to authenticate |
| Tenant ID | Required | Microsoft Entra (formerly Azure AD) Directory ID with which to authenticate |
| Schema | Optional | Name of the schema that should be used if the user belongs to a particular schema |
| Override Default Database | Optional | By default, StrongDM limits all connections to the configured database. Uncheck the box to disable this option. If this option is deselected, the value entered in the Database field is only used for healthchecks, not for user connections. When accessing the database via StrongDM, users need to explicitly pass the database name they wish to connect to in the connection string. If they do not, the value of the Username field is passed in as the database name. This is the default behavior of the database type. |
| Resource Tags | Optional | Datasource tags consisting of key-value pairs <KEY>=<VALUE> (for example, env=dev) |
Secret Store options
By default, datasource credentials are stored in Strong Vault. However, these credentials can also be saved in a third-party secrets management tool.
Options other than Strong Vault appear in the Secret Store dropdown if they are created under Settings > Secrets Management. When you select another Secret Store type, its unique properties display. Instead of the normal Client ID, Tenant ID, and Secret fields, you see versions of them that indicate that you need to enter a path. This is the path to where the secret is stored in your Secret Store location (for example, path/to/credential?key=optionalKeyName where key argument is optional).
For more details, see Configure Secret Store Integrations.
Resource status
After a resource is created, the Admin UI displays that resource as unhealthy until the healthchecks run successfully. When the resource is ready, the Health icon indicates a positive, green status.
When the resource does not display a positive status, click the resource name to go to the Diagnostics tab and check for errors.
Azure Setup
This section explains one way to create and configure a new app registration in Azure Active Directory, add an admin user, and give the user proper permissions to connect to your SQL database. If your registered app is not yet configured, please follow these steps for guidance. Note that your particular configuration may differ slightly from these instructions.
Set up your SQL database
- Sign in to the Azure portal using an account with administrator permission.
- Select Azure SQL Database from the services at the top of the page. Click Create and follow the creation wizard instructions.
- Once creation is complete, go to Azure Active Directory and click Set admin.
- Set the admin to a user that you have the password for, in the format
username@some.azure.ad.url.com. Be sure to copy the admin name for later use. - From the Networking blade, add your IP address to the firewall rules.
- Click into the database and copy the server name, which is in the format
example-server.database.windows.net.
Create a new Azure app registration
Next, you need to create an Azure app registration.
- Search for “app registrations” and click on New Registrations. Enter the display name to use for the app, and copy the display name for later use.
- Click Register and then open the newly created app registration.
- Copy the Application (client) ID and the Directory (tenant) ID for later use.
- Go to the Certificates and Secrets blade and click New Client Secret.
- Name the new client secret, and then copy the value of the client secret for later use. You may not be able to see it again.
Add the user to the database
Next, you need to add the user to the DB and grant it permissions. One tool you can use for this is SQL Server Management Studio installed in an Azure VM. Other tools that enable the same work shown below should work as well.
RDP into the VM and open SQL Server Management Studio.
In the object explorer, click Connect. Then click Database Engine.
Enter the name of the server that you saved in a previous step (in our example,
example-server.database.windows.net).Enter the admin username (in our example,
username@some.azure.ad.url.com) and the password, and connect.In the object explorer, find the database you created. Right-click on it and select New Query.
You need to run a few queries to give your app registration proper permissions. In the following examples, make sure you replace
<ENTRA_ID_USER>with the display name of your app registration.CREATE USER <ENTRA_ID_USER> FROM EXTERNAL PROVIDER;Set database role permissions:
ALTER ROLE db_datareader ADD MEMBER <ENTRA_ID_USER>; ALTER ROLE db_datawriter ADD MEMBER <ENTRA_ID_USER>; ALTER ROLE db_ddladmin ADD MEMBER <ENTRA_ID_USER>;Grant database permissions:
GRANT VIEW DATABASE STATE TO <ENTRA_ID_USER>Grant permission to specific objects:
GRANT SELECT ON [dbo].[promotion] TO <ENTRA_ID_USER> GRANT EXECUTE ON [dbo].[sp_procedure] TO <ENTRA_ID_USER> GRANT UPDATE ON [dbo].[promotion] TO <ENTRA_ID_USER>
Setup is complete. Now you can connect to the database using StrongDM.