Enterprises seek ways to effectively address the needs of dynamic, always-evolving cloud infrastructures, and StrongDM has developed a platform that is designed with built-in capabilities to support continuous compliance in AWS environments.
Posts by Category:
- Security
- Access
- DevOps
- Auditing
- Privileged Access Management
- Policy
- Zero Trust
- Compliance
- SOC 2
- Authentication
- Databases
- Identity and Access Management
- Compare
- Team
- Product
- Integrations
- Kubernetes
- AWS
- Engineering
- Productivity
- Podcasts
- Observability
- SSH
- HIPAA
- ISO 27001
- Dynamic Access Management
- Role-Based Access Control
- Secure Access Service Edge
- Webinars
- Events
- NIST
- Onboarding
- Passwordless
- Offsites
- Platform
- PCI

StrongDM releases Cedar-Go 1.0.0, delivering policy-based authorization for Go developers. Build secure, high-performance apps with Cedar’s powerful framework—now Go-native. Simplify access control, scale effortlessly, and keep security simple.

Learn why Just-in-Time (JIT) access is essential for Zero Trust security in AWS environments. Discover how StrongDM's JIT access enhances security, optimizes workflows, and ensures compliance with Zero Trust principles.
By simplifying the ability to enforce granular policies, Cedar has set a new benchmark for access control in Kubernetes, and we’re thrilled to be part of this journey. This evolution is a milestone for anyone dedicated to securing cloud infrastructure.

We are pleased to announce that Amazon has accepted StrongDM's native Go implementation of Cedar into the Cedar Policy Organization's official GitHub repository. This allows Go developers to use Cedar, a security and authorization framework built to be fast, secure, and analyzable natively in their Go programs.

re:Invent 2023 was AWS’ 12th conference, and it did not disappoint. More than 50,000 of us descended onto Las Vegas for a week of learning, networking, and discussing all things cloud. The campus was insanely large, spanning most of the Las Vegas strip, so that meant we got our steps in! We had some fun along the way, as well, at the many social gatherings, parties and amazing musical experience re:Play.
The AWS Well-Architected Framework has been a staple for many years for AWS practitioners of all sorts, including cloud architects and platform engineers. It’s a blueprint for architectural and design best practices that will lay the foundation for resilience, operational efficiency, and security on the AWS Cloud.

Since Amazon Web Services first announced it in 2011, AWS IAM has evolved to become the gateway to the AWS Cloud. Organizations cannot interact with their cloud resources and its many services without it. Identity, not networking, is the real access boundary.
Want a secure and compliant AWS environment? Then you need to audit access. Keeping tabs on who has accessed what—as well as the whens, wheres, and whys—helps you spot suspicious activities and address them promptly. Without this kind of access control, your sensitive data could be exposed to malicious actors, putting you at risk of data breaches and subsequent regulatory nightmares or service interruptions.
When it comes to cloud security, AWS follows the Shared Responsibility Model. They secure the underlying infrastructure while you protect your data, applications, and systems—including the identities that access them. Integrating AWS with a dynamic access management tool like StrongDM is key to securing identities in the cloud. StrongDM centralizes access control, while AWS offers robust security measures, contributing to a solid defense against unauthorized access.
Secure access controls must be applied universally and consistently across all your infrastructure—from the Linux boxes in your datacenter to your Kubernetes clusters in AWS. StrongDM Dynamic Access Management is uniquely positioned to provide seamless, secure access across your entire stack, simplifying access management and compliance for your legacy systems and modern cloud stack.
AWS authentication confirms the identity of users trying to access your resources, safeguarding against potential intrusions and data breaches. But weak authentication practices—like easy-to-guess passwords and single-factor authentication (SFA)—are far too common and they leave the door wide open for threat actors. Weak authentication often leads to data theft, resource misuse, financial and reputational nightmares…the list goes on. On the contrary, strong authentication measures like
We’ve just launched our AWS Management Console, adding yet another supported authentication method to improve control and auditability–so you can protect your business and improve employee productivity.
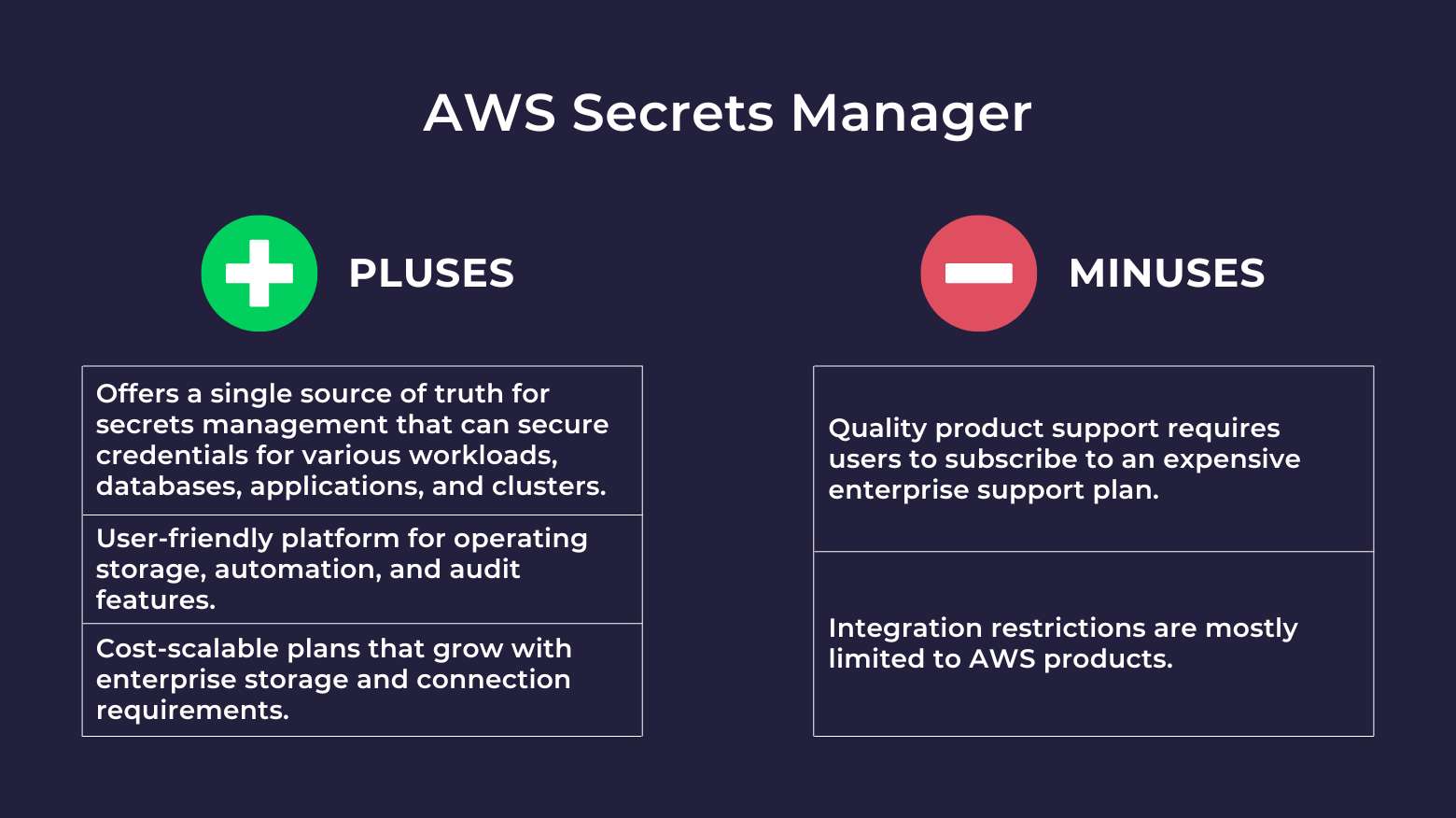
AWS Secrets Manager is a popular and highly intuitive secrets management tool that lets organizations automate secrets rotation processes and securely store, manage, and audit IT credentials. However, certain AWS Secrets Manager alternatives are available if you are looking to avoid getting tied down exclusively to AWS products or prioritize efficient user onboarding. In this product comparison guide, we evaluate AWS Secrets Manager competitors that can fill in some of its product gaps.

