Today we’re going to take a closer look at the principle of least privilege (PoLP)—what it is, why it matters, and how to implement it in your organization. Understanding the principle of least privilege is critical, as network administrators must strike a balance between ease and security—protecting network access without causing friction for users. If access is too restrictive, employees won’t be able to do their jobs. Too lax, and the door to attack is open.
Posts by Category:
- Security
- Access
- DevOps
- Auditing
- Privileged Access Management
- Policy
- Zero Trust
- SOC 2
- Compliance
- Authentication
- Databases
- Identity and Access Management
- Compare
- Team
- Product
- Integrations
- Kubernetes
- AWS
- Engineering
- Productivity
- Podcasts
- Observability
- SSH
- HIPAA
- ISO 27001
- Dynamic Access Management
- Role-Based Access Control
- Secure Access Service Edge
- Webinars
- Events
- NIST
- Onboarding
- Passwordless
- Offsites
- Platform
- PCI
Concerned that bad actors could gain access to your digital resources using stolen credentials? Don't worry, there’s a way to safeguard your employees’ account details. Modern credential management tools and policies can give you precise control over who can view keys to access your systems and how much access they may have. The information in this article will help you conquer your biggest credential management challenges. With the right knowledge and tools, you can significantly mitigate the
It’s easy to assume that individuals with privileged access will inherently do the right thing, or simply know what they’re doing when accessing systems. That isn’t always the case. Similarly, how often do you check in on your systems with privileged access to understand what they're up to?
Offboarding technical employees can be a complex and arduous process with a lot of moving parts. The key to successful offboarding is to have a clear understanding of what needs to be done, who does it, and how to monitor for any shenanigans from former employees.
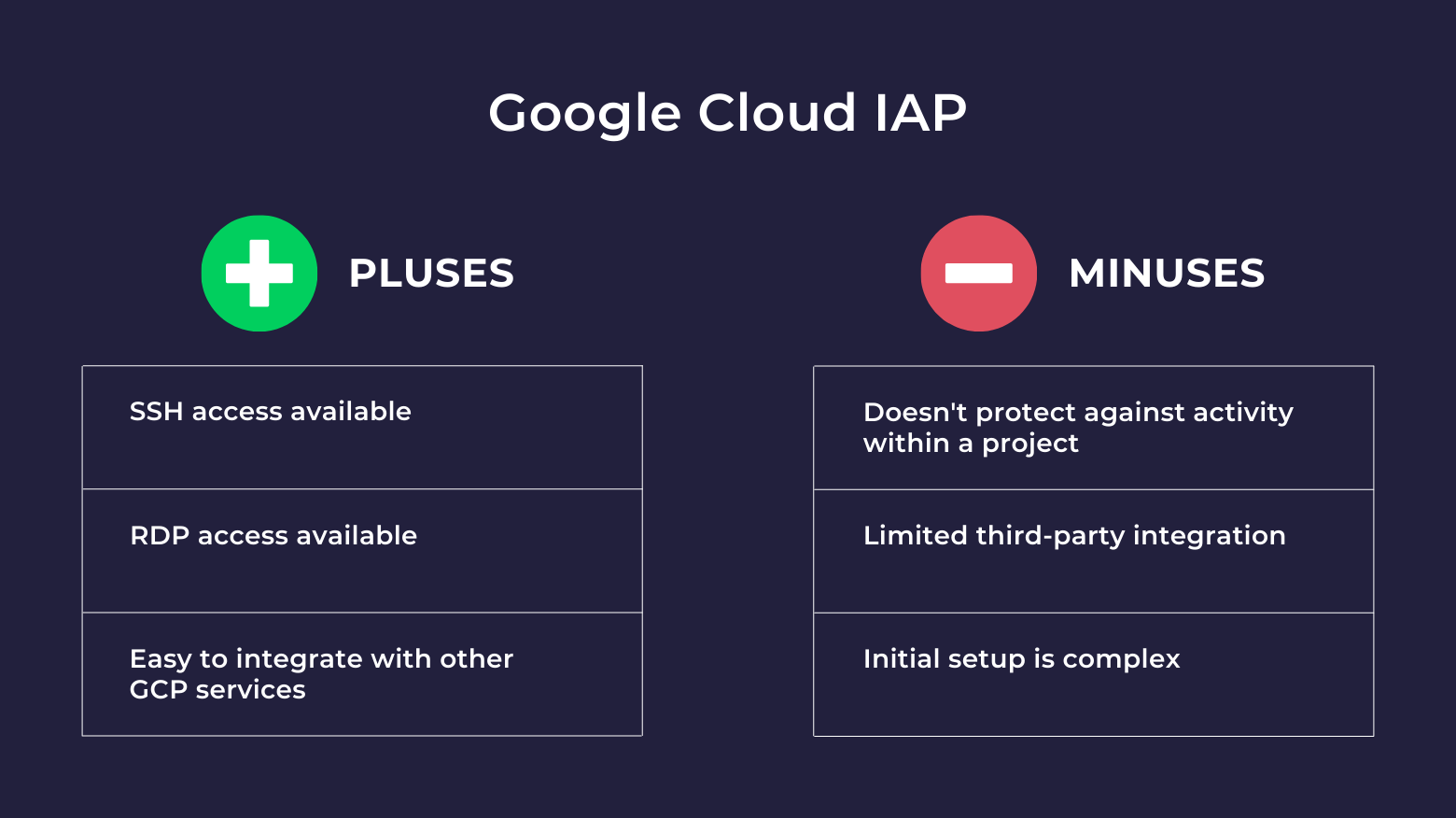
Identity-Aware Proxy (IAP) is a Google Cloud Platform service that centralizes user access to SaaS applications and other cloud resources accessed by HTTPS. IAP secures authentication for requests made to virtual machines running on GCP and other cloud-based and on-premises applications, only granting access to users you authorize. With IAP, users can connect from untrusted networks without using a VPN.
Terraform, we are a go for launch on the StrongDM provider! We are happy to announce that StrongDM has officially launched as a Terraform provider. That means that in one single configuration, you can spin up a fleet of servers, import them into StrongDM, and provision your users' access in a matter of minutes.
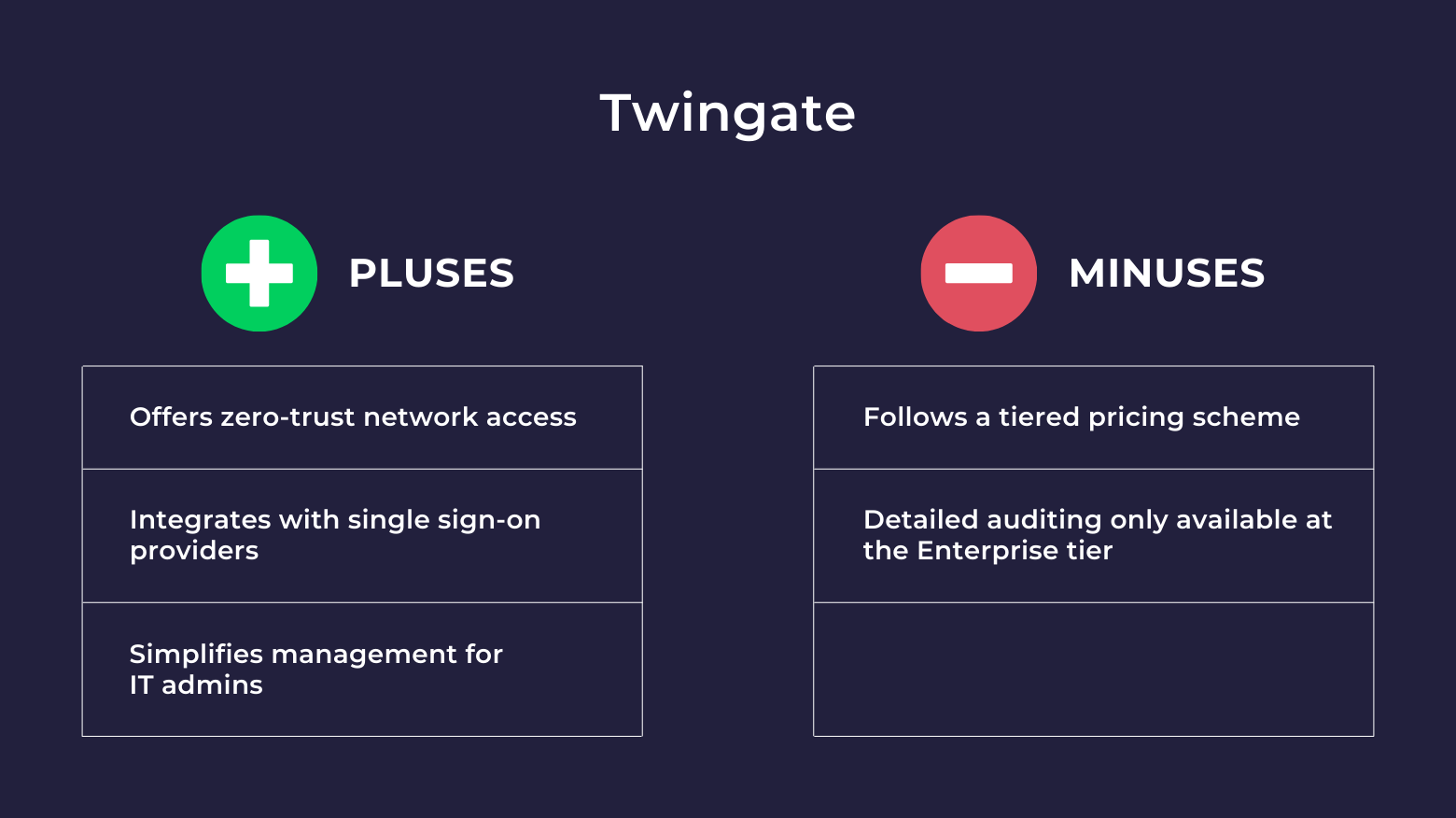
Twingate started in 2019 in response to the growing challenges of managing access for a remote workforce. The product offers a zero-trust, cloud-based solution that aims to replace Virtual Private Networks (VPNs) by providing a secure, quick-to-implement solution for IT admins and everyday users. However, if you have a distributed workforce in need of access to databases, Kubernetes clusters, cloud CLIs, switches, routers, or internal web applications, there are other tools to consider. In this
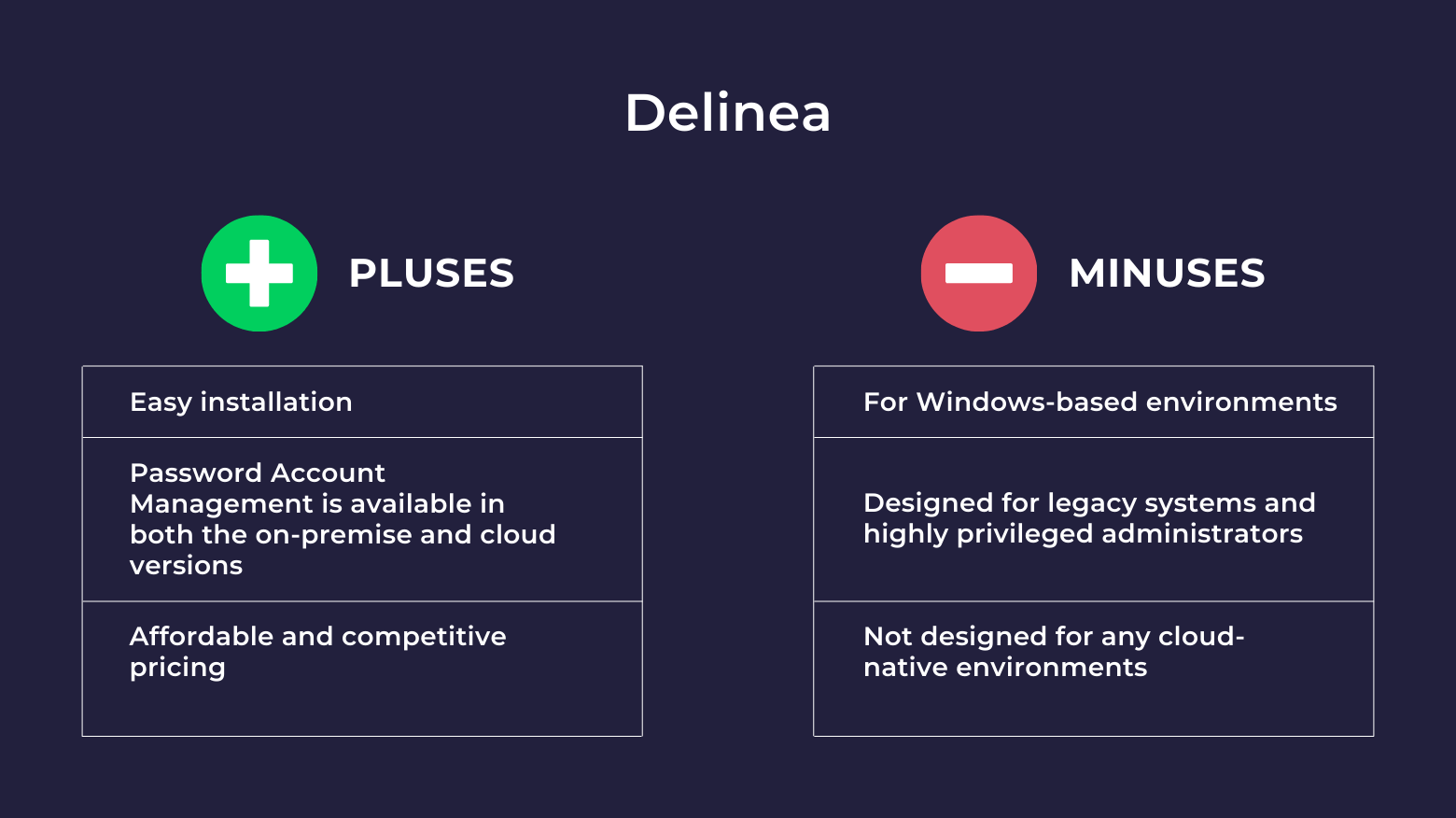
Thycotic was founded in 1996 as a consulting company and has evolved into a leading provider of Privileged Access Management (PAM). Thycotic’s Privilege Manager is a tool that allows organizations to secure access for privileged administrators (typically systems and database administrators) to Windows Servers, Linux servers, and some database management systems through a centralized authentication method. It does not secure access to modern and cloud-native databases, Kubernetes clusters, the
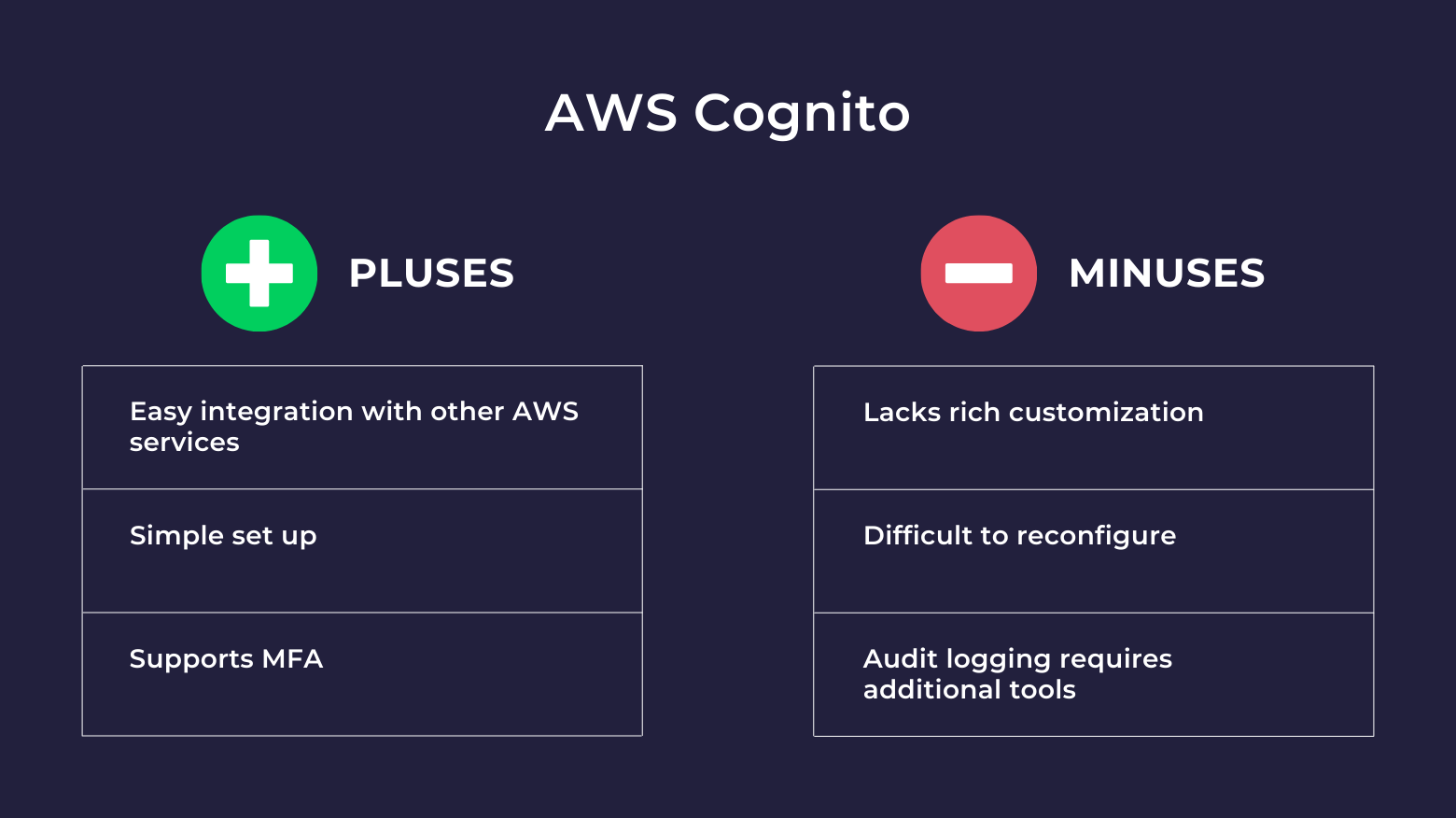
AWS Cognito is a user authentication service that lets you add access control to your web and mobile apps. Cognito manages sign-up, sign-in, password changes, token refresh, data synchronization, and updates to user account attributes. The service is initially free for AWS users, and the pricing model scales as your user base grows.
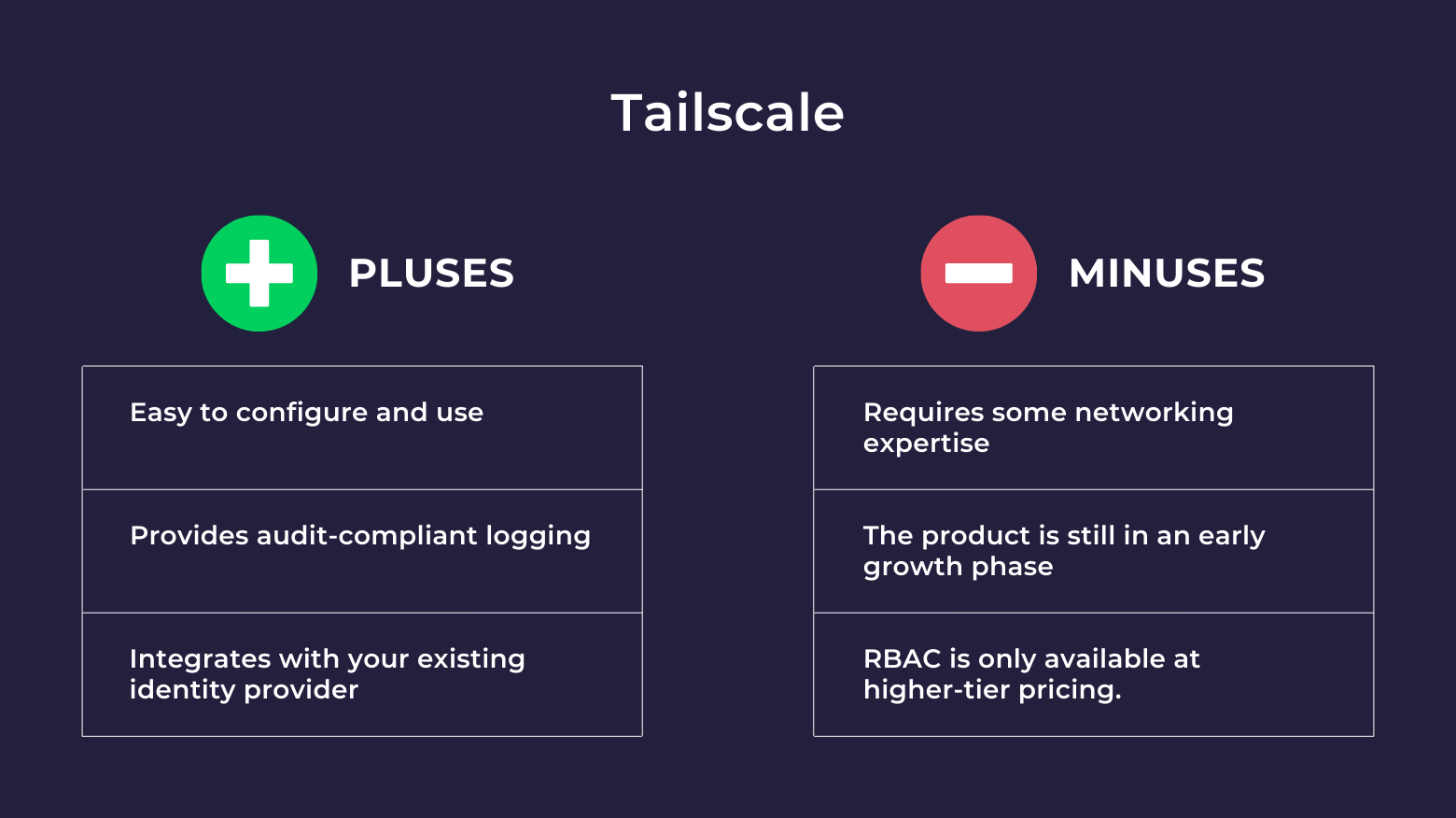
Tailscale is a zero-configuration virtual private cloud that builds secure networks for WireGuard-encrypted traffic. Tailscale replaces traditional VPNs with a coordination node that acts as a control plane to manage keys and identities. This allows you to create a secure network between cloud resources without the need for firewall configuration changes. However, if your goal is to centralize and secure access to databases, servers, Kubernetes, and more, a VPN (even a fancy modern one) may not
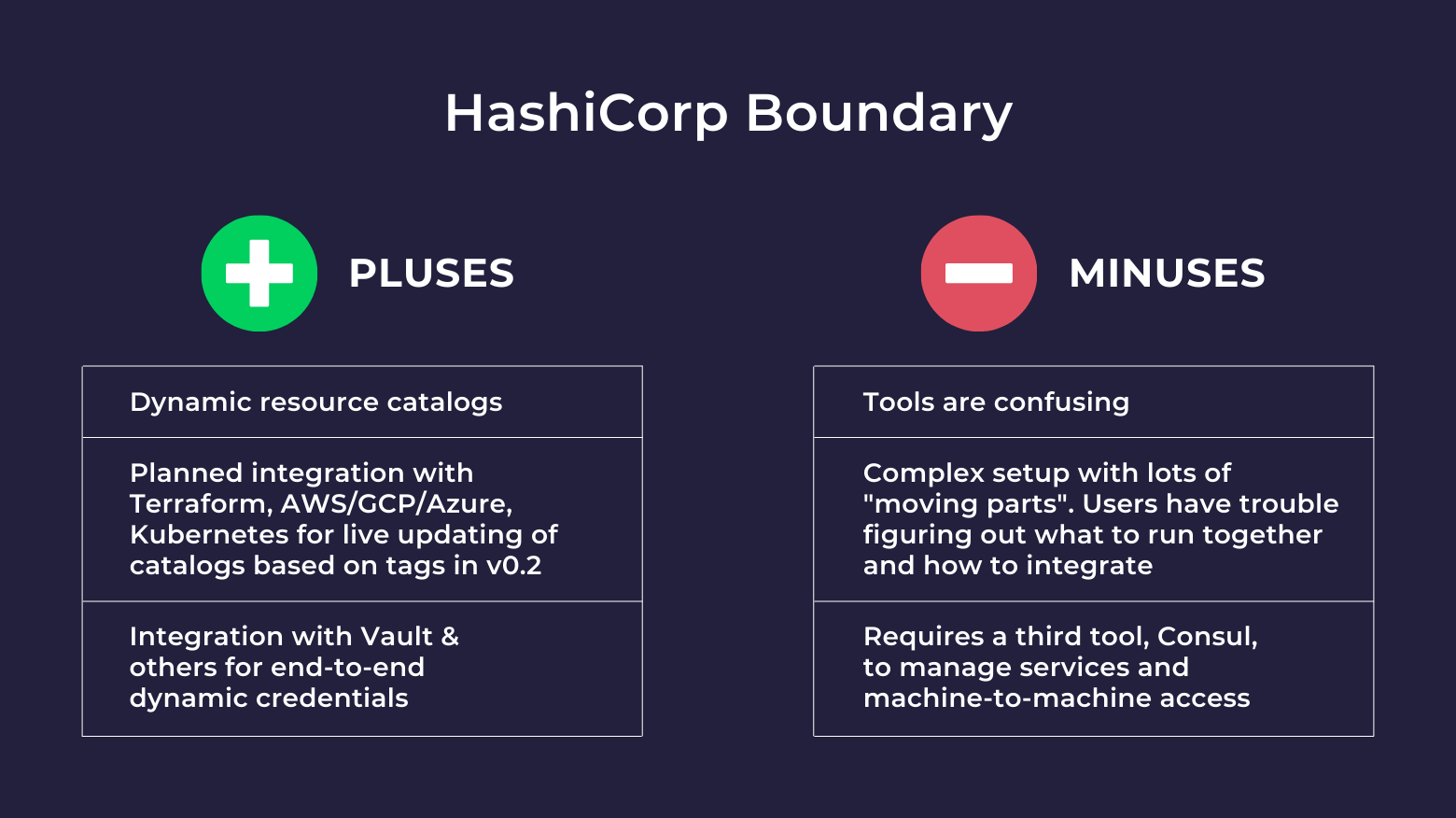
HashiCorp Boundary is an open-source identity access management (IAM) tool that facilitates secure user access to dynamic hosts and critical infrastructure across environments. However, if you need a simple and secure way to manage access to databases, Kubernetes clusters, cloud CLIs, switches, routers, or internal web applications, there are other services to consider. In this blog post, we’ll take a look at a few alternatives and discuss the strengths and weaknesses of each. First, a quick
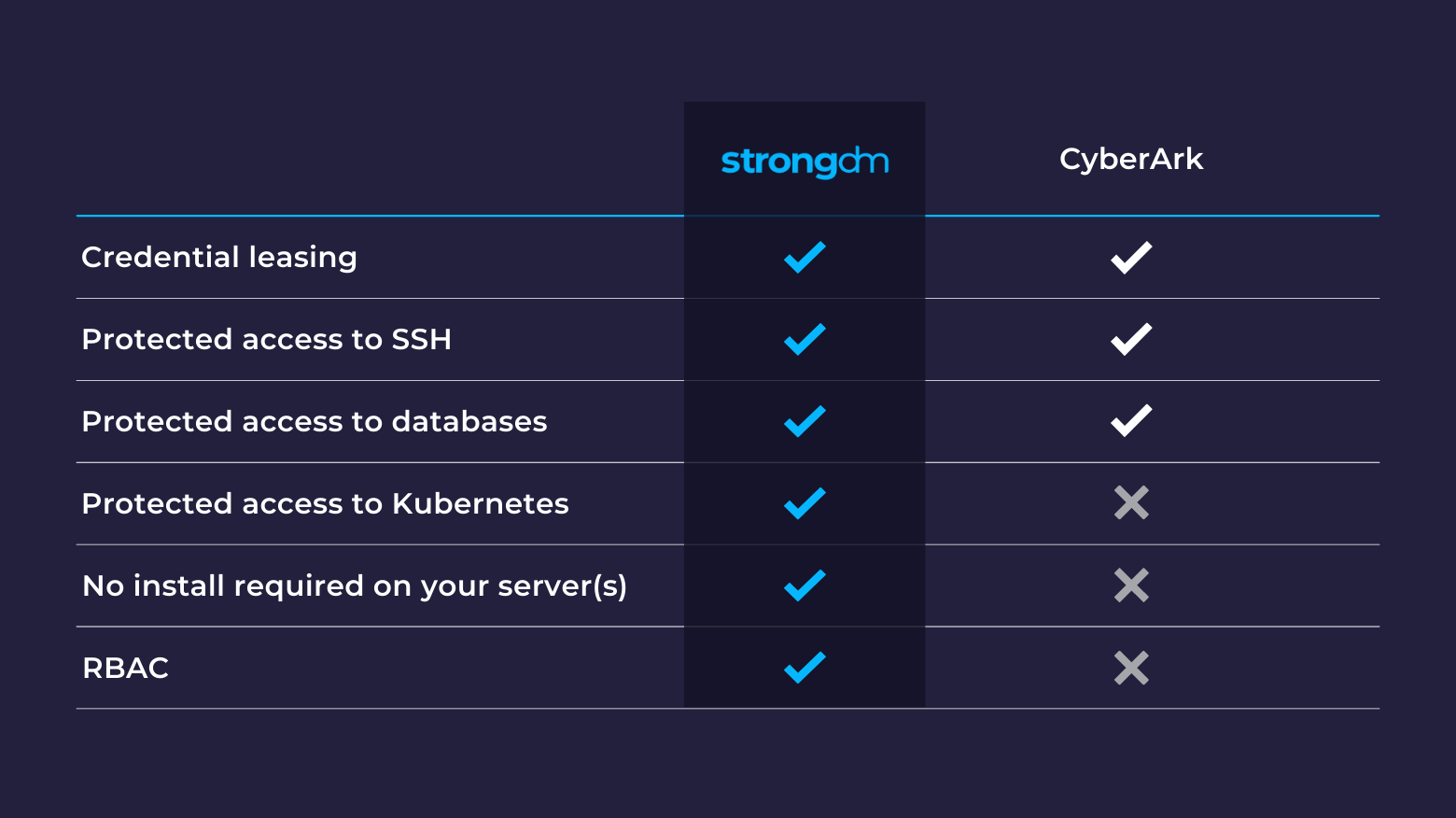
CyberArk’s Privileged Access Manager is a tool that allows organizations to secure access for privileged administrators (typically systems and database administrators) to Windows Servers, Linux servers, and some database management systems via a centralized authentication method. However, if you need to secure access to modern and cloud-native databases, Kubernetes clusters, cloud CLIs, switches, routers, or internal web applications, there are other options to consider.
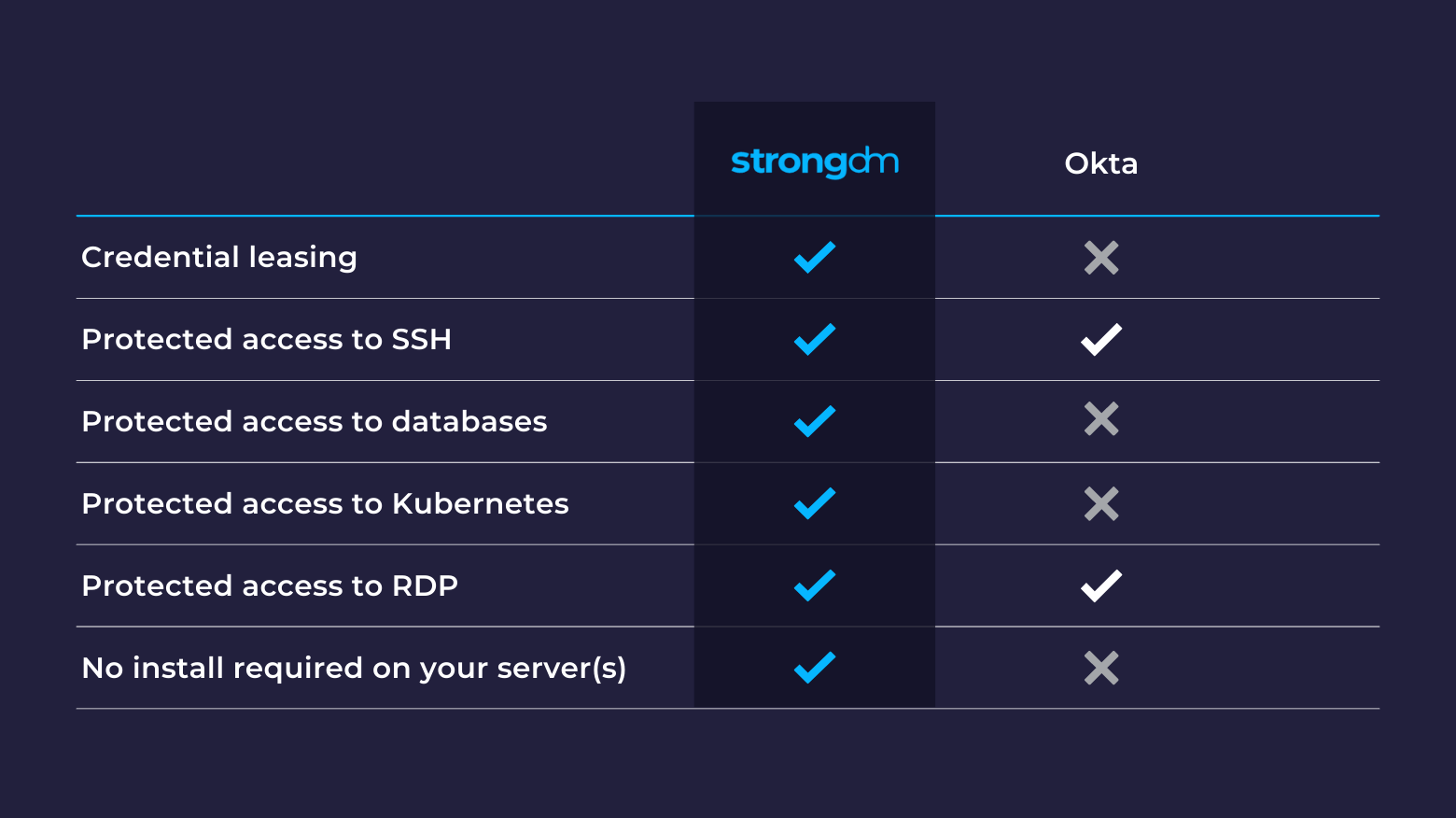
Okta’s Advanced Server Access (ScaleFT) is a tool allowing organizations to secure access to SSH and RDP servers via a centralized authentication method. However, if you need to secure access to databases, Kubernetes clusters, the cloud CLIs, switches, routers, or internal web applications, there are other options to consider.

HashiCorp Vault is a powerful secrets management tool that is well suited to automating the creation, distribution, and destruction of secrets. However, if your goal is to secure access to sensitive systems, a secrets store is not the only approach. In this blog post we’ll look at a few alternatives, with my take on the strengths and weaknesses of each approach.